In virtually every home there now resides at least one device that connects to the Internet. Originally home computers were the only things we owned that could connect to the Internet. These could be, and often were, powered off when not in use. In today’s connected world more and more devices are introduced into home networks and many are never powered off.
Mobile phones are certainly the most common Internet-enabled device with over 25 million smartphone users predicted for 2018 in Canada alone. The idea of these devices being simply a portable telephone is very outdated. In reality a smartphone is a computer that is continually connected to the Internet and many other devices are following suit.
Big box technology stores now have multiple aisles dedicated to home technology. Thermostats, surveillance cameras, light switches and bulbs can all be brought home and connected to a home network.
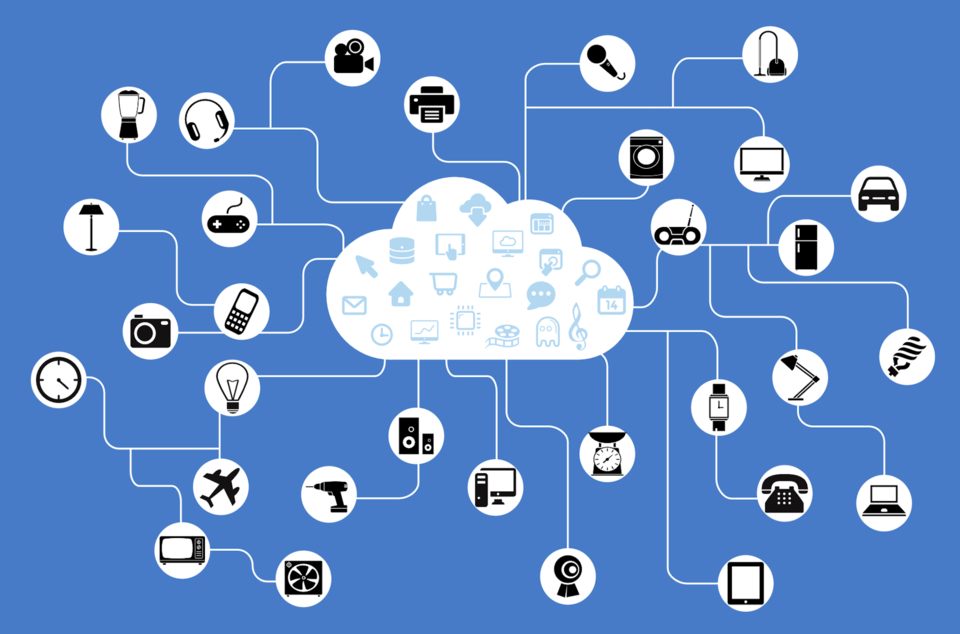
For the right price your home can play host to a refrigerator that keeps track of your groceries and places an order for you, automatically, whenever you run out of milk. These “Internet of Things” devices, or “IoT”, are generally managed via a smartphone application and secondarily obtain access to the Internet.
Why should this be a problem for anyone? The reality is that every network needs protection from the rampant dangers found on the Internet. Security software needs to be installed on computers to ensure that they stay safe while connecting to the things in the outside world.
IoT devices connect to your network the same as a computer and they all connect to other networks via the Internet. Some devices, like security cameras, may store data in a cloud environment. Other items may simply connect to their manufacturers’ servers to report statistics or check for software updates. When purchasing IoT devices we don’t have the luxury of installing a security application to protect them when they connect to networks outside of the home.
As these devices cannot be upgraded with third-party security software, and have no monitors or displays for us to see what they are doing, they have completely unsupervised access to the Internet. While this hardly makes them dangerous, they do pose a risk due to the centralized nature of their communications.
Nefarious computer users seek out vulnerable machines to take control of. When a sufficient number of machines are under their control these users can use them all simultaneously to launch attacks against other websites or services.
The challenge in this is to gain and maintain control over many machines on many different networks. Since IoT devices all connect to remote systems for software updates a malicious user needs only focus on the services that these devices communicate with rather than gaining control of these devices individually.
On Oct. 21, 2017 a large attack was launched against a company called Dyn which manages address lookups for a large portion of the Internet. The attack was successful and caused significant disruption in Internet traffic to a number of websites. The reason the attack was successful was due to the large number of improperly secured IoT devices that exist on the Internet.
Vulnerabilities in these devices were exploited to use large number of them to simultaneously to attack Dyn’s Domain Name Services that provide address lookups for Internet traffic rendering many websites virtually useless, in some cases for hours. Thanks to unsecured IoT devices the Internet saw a 91 per cent increase in these types of attacks in 2017.
No device should be connected to the Internet without first ensuring it can be managed and secured. Talk to your friendly neighbourhood computer guy for assistance in making sure that you stay safe and none of your equipment poses a threat to you or anyone else.
Kevin Davison is a Guelph-based computer consultant for Kadence Solutions. He has over 20 years of experience in computer and network management. Kevin also possesses expertise in telecommunications systems, home automation, security and various residential and commercial electronics.
This Content is made possible by our Sponsor; it is not written by and does not necessarily reflect the views of the editorial staff.